BitProof
Whitepaper
BitProof: Bitcoin-Anchored Timestamping for Files and Web Archives
Technical design for verifiable digital timestamps
Version 2.1 · February 2026
The Problem
We live in an era where digital content can be created, modified, and deleted without trace. AI-generated deepfakes are indistinguishable from reality. Screenshots can be fabricated. Websites change or disappear. There is no native mechanism in the digital world to independently verify that a specific piece of content existed in a specific form at a specific time.
The consequences are profound: whistleblowers can't reliably show they had evidence before an investigation began, researchers can't establish prior art with mathematical certainty, journalists can't reliably demonstrate a website said what it said before it was edited, and ordinary people can't reliably document they created something before someone else claimed it.
The Solution
BitProof anchors the SHA-256 hash of any digital content to Bitcoin's blockchain via the OpenTimestamps protocol. This creates a mathematical proof that the content existed in exactly that form at the time the hash was included in a Bitcoin block, without requiring trust in any organization, including BitProof itself.
The key properties of this approach:
- Verification-based. Proofs are anchored to Bitcoin and can be checked independently with standard OpenTimestamps tooling or the Verify Proof page.
- Privacy-preserving. Files are hashed client-side. Only the hash, a 64-character string, ever touches our server. We never see your content.
- Durable. Verification data is stored in the proof bundle and anchored to Bitcoin block history.
- Independently verifiable. Anyone can verify a proof using standard OpenTimestamps tools. No dependency on our service.
- Stateless. No proof database, no user accounts, no retained file copies. You keep your proof bundle. Standard operational logs may exist.
Use Cases
BitProof is most useful anywhere digital evidence can be edited, deleted, or disputed later. It is designed for practical proof of existence and integrity, not platform trust.
- Journalism: Preserve public statements before they are edited or removed.
- Research and prior art: Establish that findings, drafts, or datasets existed at a known point in time.
- Scientific reproducibility: Timestamp protocol versions, dataset snapshots, and analysis code used in reported results.
- Legal support: Capture contracts, terms, and web evidence with cryptographic timestamps.
- Whistleblower workflows: Show evidence existed before an investigation or disclosure event.
- Creator provenance: Document when work product existed in a specific form.
- Collaborative attribution: Use optional authorship signatures to show which signing key approved an artifact version.
- Business intelligence: Track policy pages, product claims, and competitor changes over time.
- Public accountability: Preserve social or web posts that may later be altered or deleted.
How It Works
File Timestamping
- User selects a file in the browser
- The file is hashed locally using SHA-256 (Web Crypto API)
- Only the 64-character hex hash is sent to BitProof's server
- The server submits the hash to OpenTimestamps calendar servers
- OpenTimestamps aggregates hashes into a Merkle tree and anchors the root to a Bitcoin transaction
- (Optional) The browser can add a local Ed25519 authorship signature to the bundle manifest
- The user downloads a
.bitproofbundle containing a manifest and the OTS proof - Within ~1-2 hours, the proof is confirmed in a Bitcoin block
Web Archiving
- User enters a URL
- The server captures a full-page screenshot (PNG), the HTML source, and a PDF rendering via a headless browser
- Each captured file is hashed, and the hashes are combined into a deterministic bundle hash
- The bundle hash is submitted to OpenTimestamps
- The user previews the captured content inline, then downloads a
.bitproofbundle containing all captured files, manifest, and OTS proof
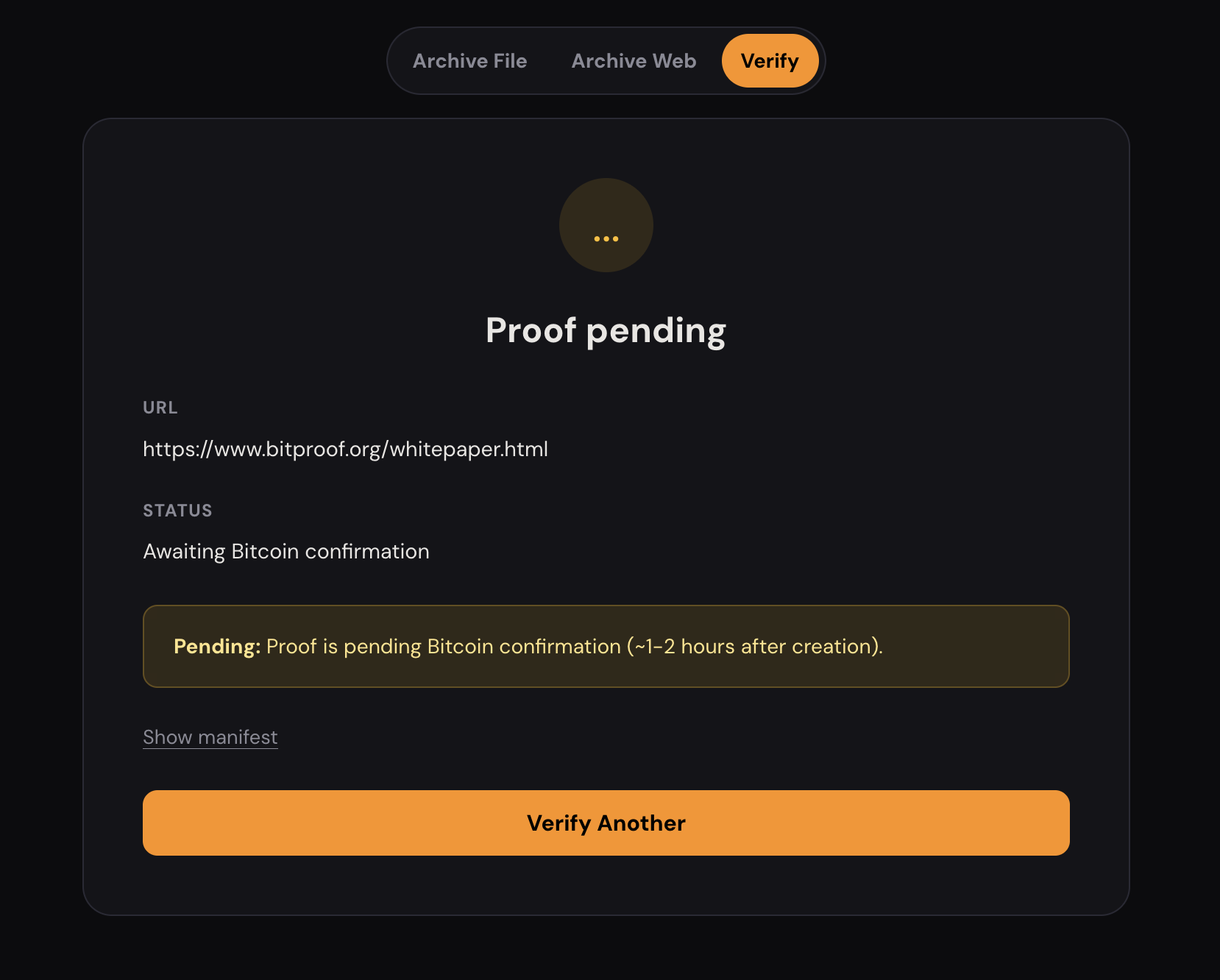
Verification
Practical path: open Verify Proof, upload your original content and the .bitproof file, and confirm the result.
- User uploads the original file (or archive bundle) and the
.bitproofproof - The system re-hashes the original content and compares it to the hash in the proof
- The OTS proof is verified against Bitcoin's blockchain
- If authorship metadata is present, the Ed25519 signature is validated against the signed hash target
- If both match, the proof is valid, and the content existed in that exact form at the proven time
The .bitproof Format
A .bitproof file is a standard ZIP archive containing:
{
"manifest.json" // Metadata, hashes, proof status
"proof.ots" // OpenTimestamps proof file
"screenshot.png" // (archives only) Full-page screenshot
"page.html" // (archives only) HTML source
"page.pdf" // (archives only) PDF rendering
}
The manifest is the machine-readable receipt inside every bundle. In practice, most readers only need three things:
- Hash target: what was timestamped (`file.hash` for files or `bundle.hash` for archives)
- Proof block: OTS method + status
- Authorship (optional): key-control signature metadata
Abridged manifest example:
{
"version": "2.0",
"type": "bitproof-timestamp" | "bitproof-archive",
"created_at": "ISO 8601 timestamp",
"file": { // file timestamp flow
"hash": "SHA-256 hex",
"algorithm": "SHA-256"
},
"bundle": { // archive flow
"hash": "SHA-256 of concatenated file hashes",
"algorithm": "SHA-256"
},
"proof": {
"method": "opentimestamps",
"status": "pending" | "confirmed"
},
"authorship": { // optional
"version": "1",
"algorithm": "Ed25519",
"key_id": "ed25519:...",
"public_key": "base64url",
"signature": "base64url",
"signed_payload": { "file_hash" | "bundle_hash" },
"created_at": "ISO 8601 timestamp"
}
}
Full field-level schema is documented in docs/spec/SPEC.md.
Architecture
User's Browser BitProof Server Bitcoin
────────────── ─────────────── ───────
File -> SHA-256 ──hash──> OpenTimestamps stamp ──anchor──> Block
│ │
└─(optional Ed25519 sign)───┘
Server response: .bitproof ZIP
URL ─────────────> Playwright capture
│ screenshot.png
│ page.html
│ page.pdf
↓
Bundle hash -> OTS stamp ──anchor──> Block
│
Server response: JSON preview + .bitproof ZIP
- Timestamp flow: browser hashes locally, server timestamps that hash via OTS, then returns a proof bundle.
- Archive flow: server captures page artifacts, timestamps the deterministic bundle hash via OTS, then returns preview + proof bundle.
The backend is fully stateless. It uses temporary directories that are deleted after each response. There is no database, no file storage, no user accounts.
Security Model
BitProof can prove: integrity and existence timing. If the hash matches and the OTS proof verifies against Bitcoin, that content existed in that form on or before the confirmed block time.
BitProof does not prove: legal identity, factual truth, or exclusive ownership. Optional authorship signatures prove control of a signing key, not real-world identity.
Assumptions: Bitcoin history remains available, SHA-256 remains collision-resistant, and your local device hashes content correctly. Independent verification does not require trusting BitProof infrastructure.
Why Bitcoin
Bitcoin is a widely used proof-of-work chain with long operational history and broad tooling support. Using OpenTimestamps on Bitcoin keeps proofs low-cost through Merkle aggregation and allows verification with standard OTS tooling.
Future Directions
- Extension distribution maturity: Store approval, update channels, and release automation across major browsers
- Stronger authorship claims: Optional domain/wallet challenge binding on top of current key-control signatures
- Batch timestamping: Timestamp multiple files in a single proof
- CLI tool: Local-first operation for scripted and offline-friendly workflows
Philosophy
BitProof focuses on simple, auditable timestamping for digital files and captured web content. The goal is to make independent verification practical without requiring data custody by this service.
Verify independently.
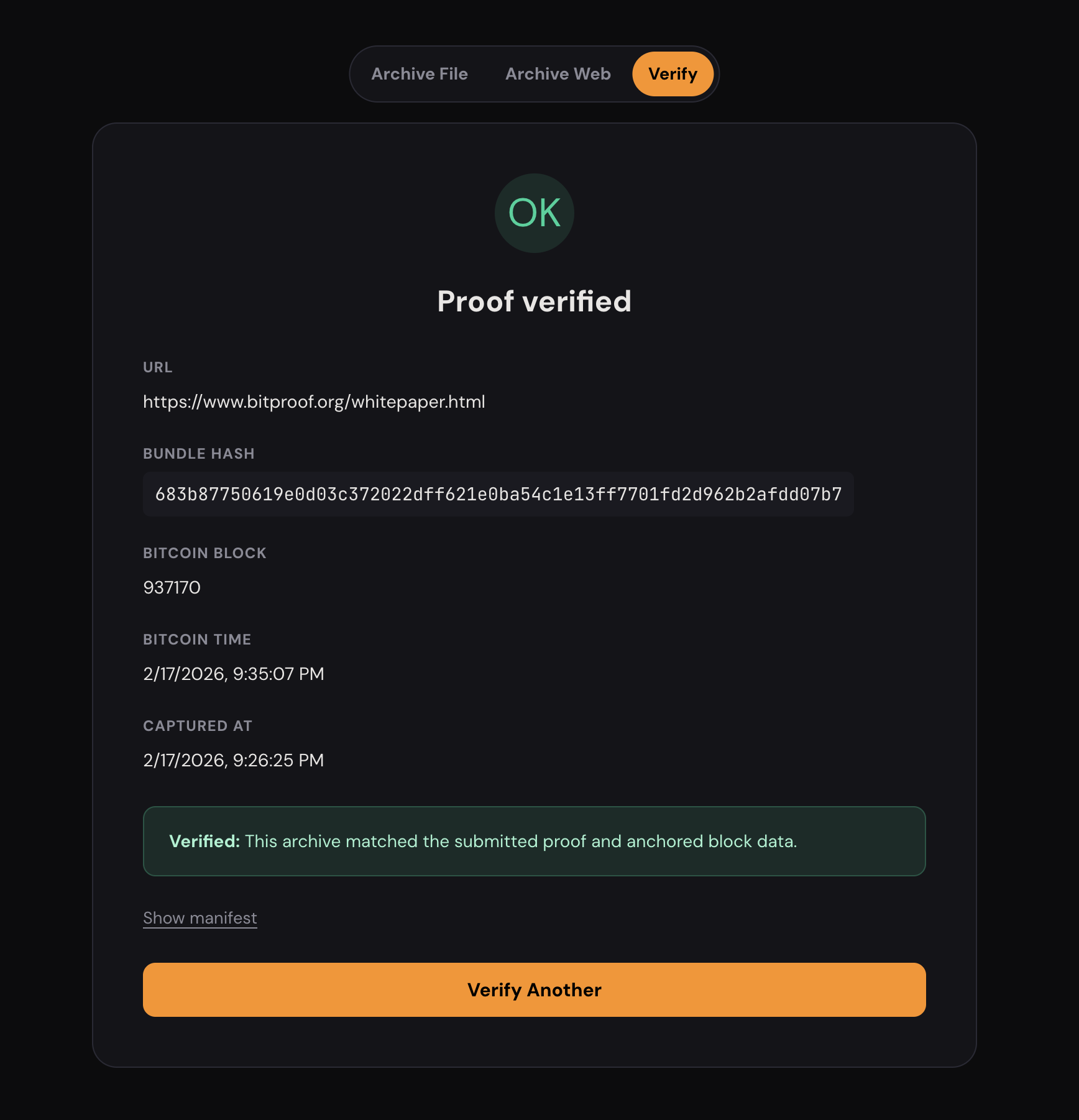
Whitepaper Verification Record
Confirmed on BitcoinThis page was archived using BitProof. The record below is the current canonical archive for this whitepaper page.
Verify flow: open Verify Proof and upload the original archive bundle.